Four of the Biggest Data Security Risks for Businesses
 14
14 Jan
Data breaches have made plenty of headlines the past few years, and malicious attacks on organizations large and small will continue to impact businesses in many ways.
We’ve seen how data security issues maligned household names from Facebook and FedEx to Marriot and Macy’s. Even the U.S. Airforce was the victim of a military data breach when a hacker who gained access to a captain’s computer stole classified information and sold it on the dark web.
Trust is an extremely important part of any business relationship. Your customers and the people you work with trust you with their data. As an I.T. professional, you’ve been entrusted with the task of helping protect that data. That means finding partners you can trust to help keep sensitive data out of the wrong hands.
Here’s a look at a few of the biggest data security threats businesses face today and what measures I.T. leaders should consider. As you’ll see, these risks can come in familiar yet more-complicated forms, and they can emerge from technology both new and old.
1. Continued Rise of Cybercrime and Ransomware
Data is valuable. So valuable, cybercriminals may threaten to hold it for ransom. Cybercrime is big business. In fact, a study from Bromium estimates it generates as much as $1.5 trillion per year. The study found $500 billion of that revenue comes from theft of trade secrets and intellectual property (IP), and another $160 billion comes from trading stolen data.
You may hear about data breaches at large corporations in the news, but research shows smaller companies are getting hit as well. Verizon’s 2018 Data Breach Investigations Report found 58 percent of cyberattacks target small businesses.
Big companies may lead to a bigger payoff, but I.T. security solutions at small and mid-sized businesses (SMBs) can be easier to penetrate. These attacks, however, are hard for smaller businesses to recover from. Verizon’s report found 60 percent of SMBs that experienced a cyber-attack were unable to sustain the business for more than six months, with the cost of dealing with the breach reaching $600 thousand or more.
As an I.T. professional, you need to help your organization develop a cybersecurity plan with methods for encrypting data, authenticating users, and authorizing access to your network. It’s also important to educate employees on the risks so they are vigilant and spot suspicious activity that could put the company’s data at risk. The Ponemom Institute found negligent employees were the top cause of data breaches at North American businesses.
2. Increased Connectivity = Increased Risk
Technology keeps moving forward, which means both honest organizations and crooked criminals are finding new ways to get work done.
In many markets, the industrial internet of things (IoT) offers a lot of promise. There’s also machine learning and artificial intelligence bringing new technological solutions to the business world. Connected equipment, cloud storage, and migration of key systems to the cloud mean companies are producing, recording, sharing, and leveraging more data than ever. But, as Cisco Chief Security Architect Michele Guel stated in an interview with TechRepublic, this technology comes with concerns.
“With the internet of things, which has been around for a while, we’ve seen the threat landscape exponentially increase … The industry as a whole is learning how do we secure IoT for one, because that’s the focus now.”
Guel notes that there are sensors in many different things, from consumer products, such as glasses and watches, to automated equipment in smart factories. They make life and work easier and provide important insights. The problem she sees is that those sensors are not always as secure as they should be.
Smart devices can be an entryway for attacks, or they could be leaking sensitive data that gets picked up by the wrong people. Guel says older forms of cyber attacks are “new again” because of these security vulnerabilities. Thankfully, companies like Cisco are recommending and developing ways to secure industrial IoT, protecting the data being passed through networks.
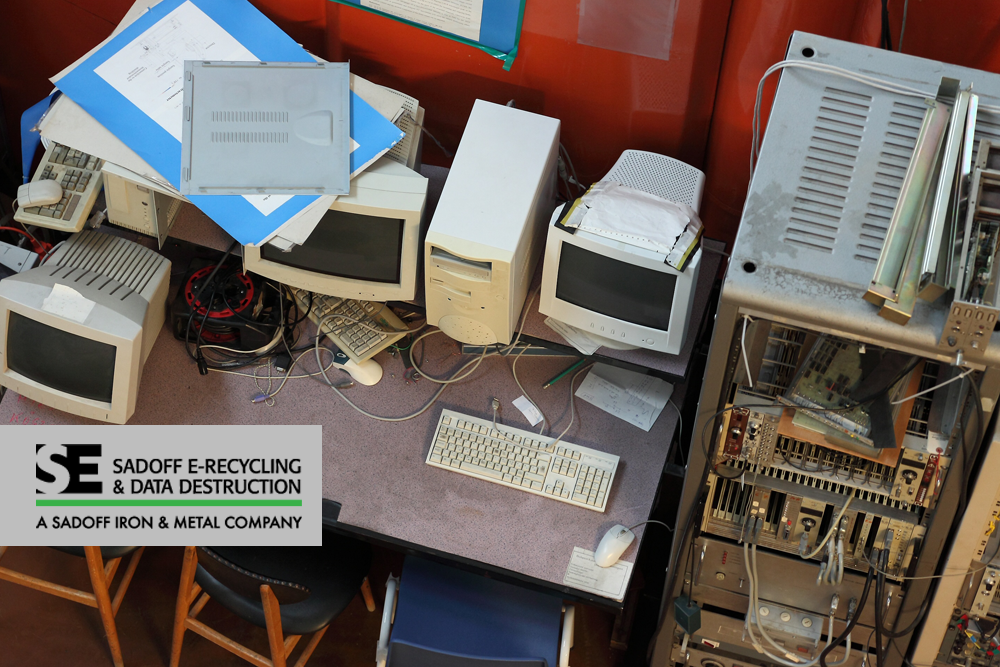
As your organization implements new technology, you will inevitably have old technology to replace, including devices storing sensitive data. That’s just one reason why businesses need a reliable electronics recycling and a secure data destruction partner.
3. The Mobile Workforce and Bring Your Own Device (BYOD)
Yet another way we’ve become more connected is the blurring of lines between work and personal life. More people are telecommuting/working from home and these people are often using personal devices in their jobs.
The risk here is that sensitive corporate data could be leaving your building and your network along with these employees and their mobile devices. According to Computer Weekly, more than 90 percent of I.T. leaders from 500 organizations questioned in a recent survey said the mobile workforce presented growing security concerns and that the emergence of BYOD (bring your own device) increases mobile security risks.
The I.T. department should lead the way in developing BYOD policies and mobile device management (MDM) solutions. Potential policies include:
- Placing limitation on free Wi-Fi hotspots
- Device and user authentication
- Multi-factor authentication to access company applications
- Requiring use of a virtual private network (VPN) on Wi-Fi
You’ll need to decide what’s right for your organization and find ways to educate employees on how to mitigate mobile security risks when using their devices for work.
One reason some employees choose to use their own devices rather than company issued laptops, desktops, and mobile phones, is that they’ve invested in newer technology that may be faster, easier to use, and may help them work efficiently. Companies that provide employees with updated devices may see fewer people using their own phones and laptops for work, which decreases some of the risk. Of course, you’ll need to be sure to have an e-recycling and data destruction plan for the old devices and hardware.
4. Legacy Systems and Obsolete Hardware
Legacy systems and software applications that are behind on updates weaken cybersecurity. That’s something every I.T. pro knows.
While old hardware may not be at the top of your list of data security concerns, according to Techopedia, it is one of the most commonly overlooked risks among businesses. Senior editor Tara Struyk writes:
“Companies face many risks when it comes to data breaches. Some occur digitally and some occur when a piece of hardware is stolen from the site, but the one we hear about least often is the risk of disposing of I.T. assets.”
According to Security Magazine, legacy hardware and software doubles the risk of a data breach. The longer you go without updating, the more vulnerable your organization becomes.
If the offices of your I.T. department are littered with archaic desktops, outdated laptops, and old BlackBerry phones, you need to do something about it. Letting obsolete I.T. equipment sit in storage is a significant security concern. As Sadoff’s Chad Hayes explains, blame for data breaches connected to obsolete technology will likely fall on I.T. staff.
“Without a reliable and trusted partner with whom to recycle electronics, the responsibility of securely disposing and destroying data often falls on I.T. That’s not only tedious work, but a massive security obligation that falls on the shoulders of I.T. personnel.”
Your I.T. department can find that reliability and peace of mind with Sadoff E-Recycling and Data Destruction. Our comprehensive checklist ensures safety and responsibility whether you choose e-recycling, or remarketing I.T. assets or refurbishing old technology. Hard drives and storage devices are not simply wiped, they are effectively destroyed, which is why Sadoff E-Recycling and Data Destruction guarantees data protection.
Sadoff E-Recycling and Data Destruction takes your data security seriously. We adhere to NAID requirements and are proud to be an ISO-certified electronics recycler. Contact us today to find out more about how we can help your company with e-recycling and data destruction needs.
Tags: electronic data, electronics recycling, Enterprise IT Asset Destruction, Finding an E-recycler, technology refreshCategorized in: Data Security, Electronics Recycling, IT Equipment
 Google map directions
Google map directions
 Google map directions
Google map directions
 Google map directions
Google map directions
 Google map directions
Google map directions
 Google map directions
Google map directions
 Google map directions
Google map directions
 Google map directions
Google map directions
